In today’s highly interconnected, digital business landscape, ensuring secure and efficient user authentication has become paramount. Without it, organizations not only risk offering poor access experience to users but also stand to make available sensitive information to unauthorized parties. This could be especially true of large organizations with complex security needs.
Streamlining User Authentication for Enhanced Security
Introduction
How to Integrate Okta with Tableau
Given this, it is no surprise that many organizations today implement Identity and Access Management (IAM) solutions like Okta to manage user access and ensure security. Okta is a leading IAM provider that offers a range of features and integrations to cater to different business needs. One of these integrations is with Tableau. In this blog, we’ll explore how you can integrate Okta and Tableau to achieve secure and seamless user authentication.
Configuring SAML for Tableau Cloud Using Okta as an IDP
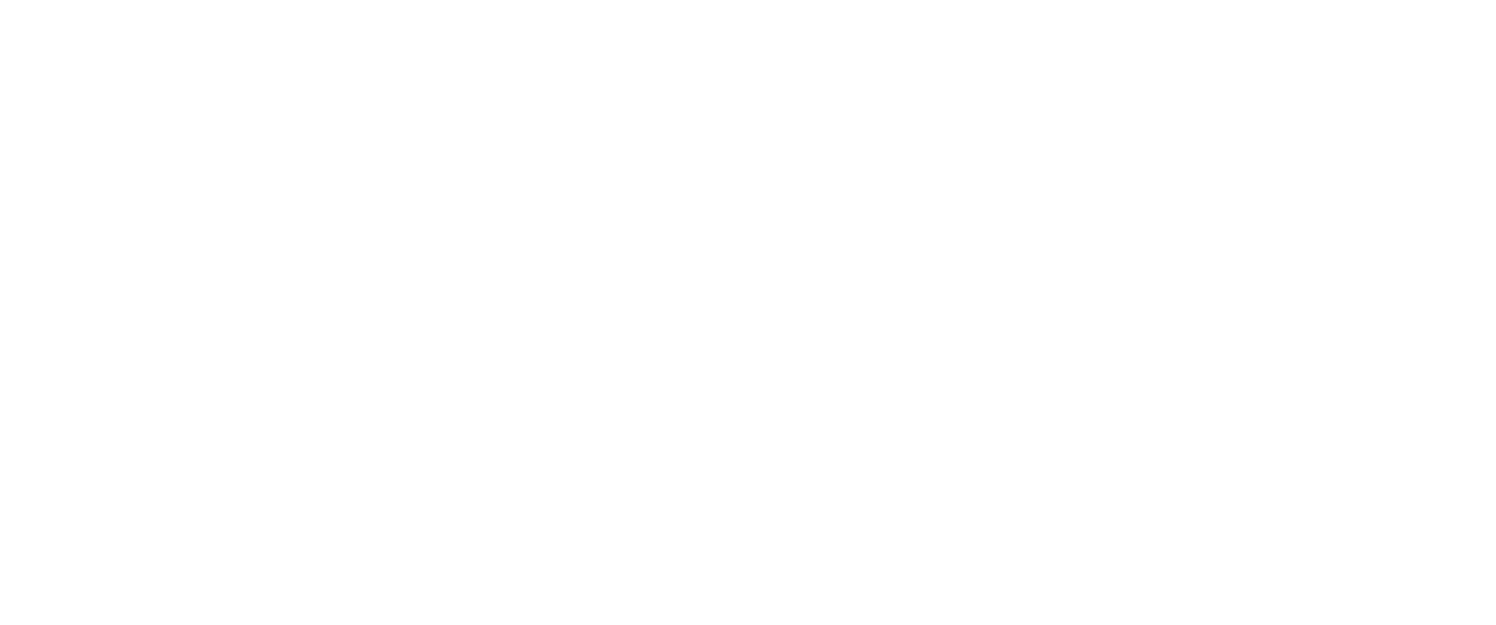
1. Sign into your Tableau Cloud site as a site administrator and select Setting >Authentication, and in the Authentication tab, select Enable an additional authentication method. Post this, select SAML and then Edit Connection.
2. Open a new browser tab, and sign into your OKTA Administrator console.
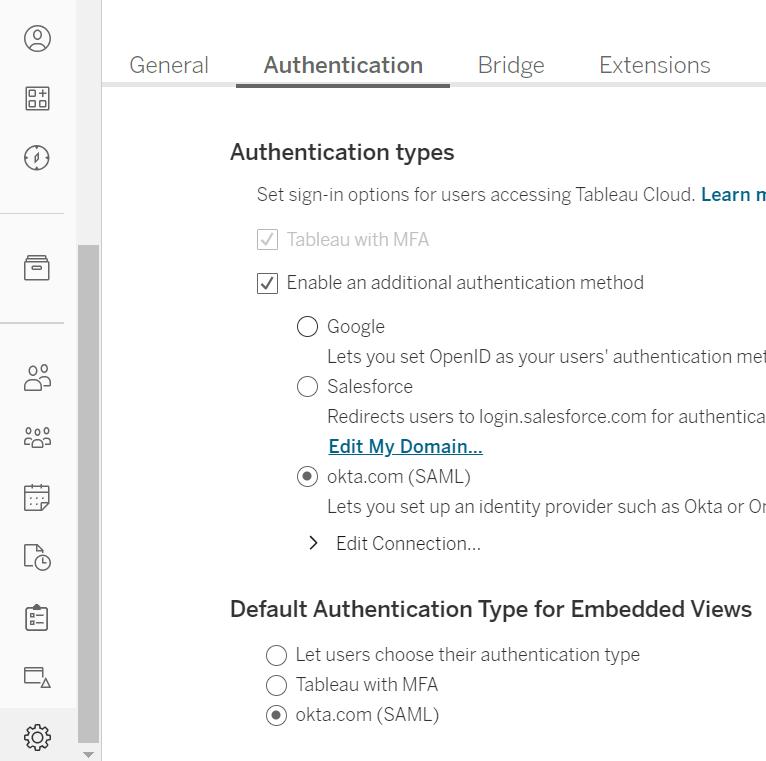
3. In the Applications tab, click on the Add Application button. Search for Tableau, and then add the Tableau Cloud application. This opens the General Settings tab. Here, add the name of your site.
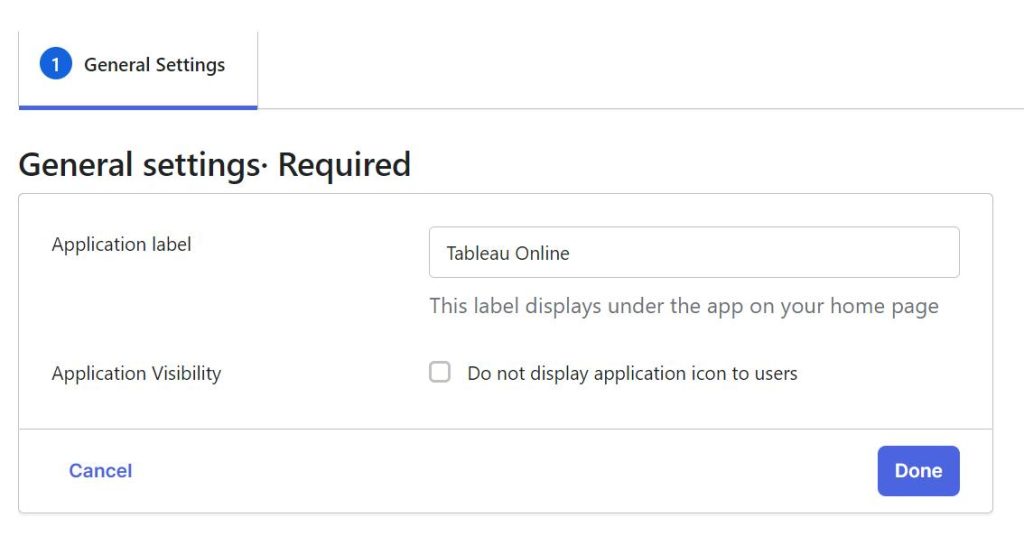
4. Click Done to open the Assignments tab.
5. Click Assign > Assign to Groups and click the Assign button beside each group you want to approve for single sign-on access to Tableau Cloud.
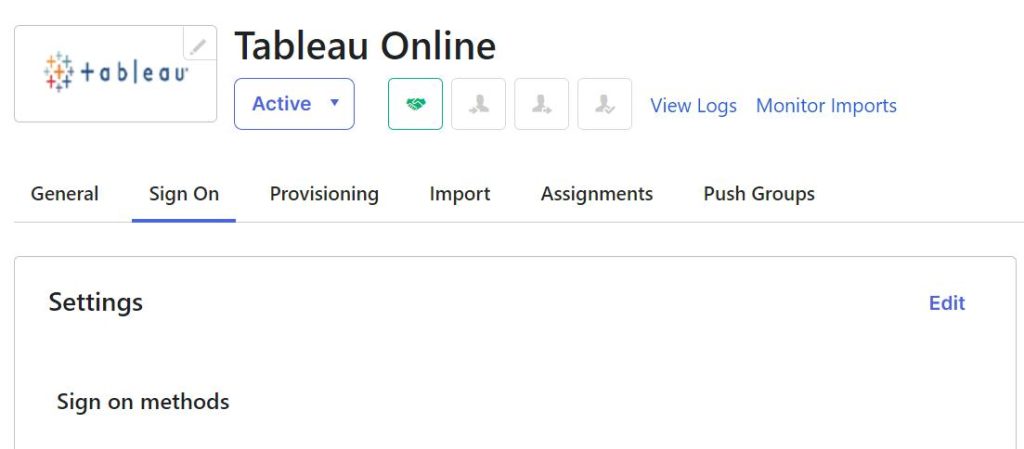
6. Select the Sign On tab and click Edit.
7. Switch to the tab where you opened the Tableau Cloud SAML configuration settings, and in Step 1 of those settings, select and copy the Tableau Cloud entity ID and ACS URL.
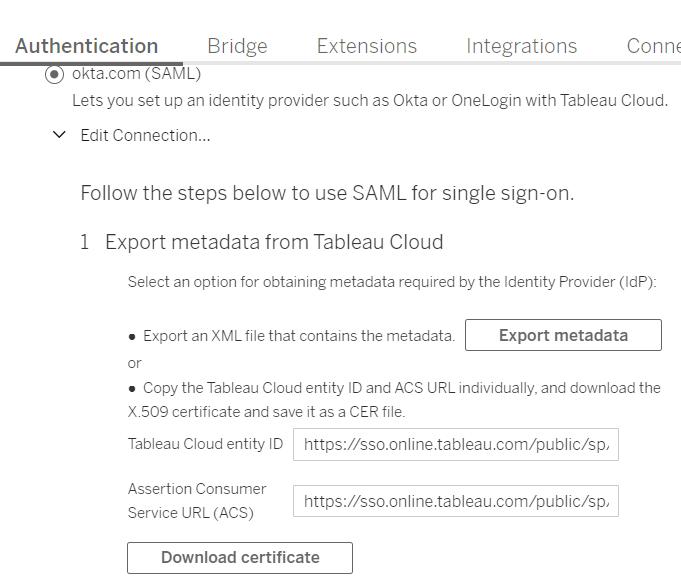
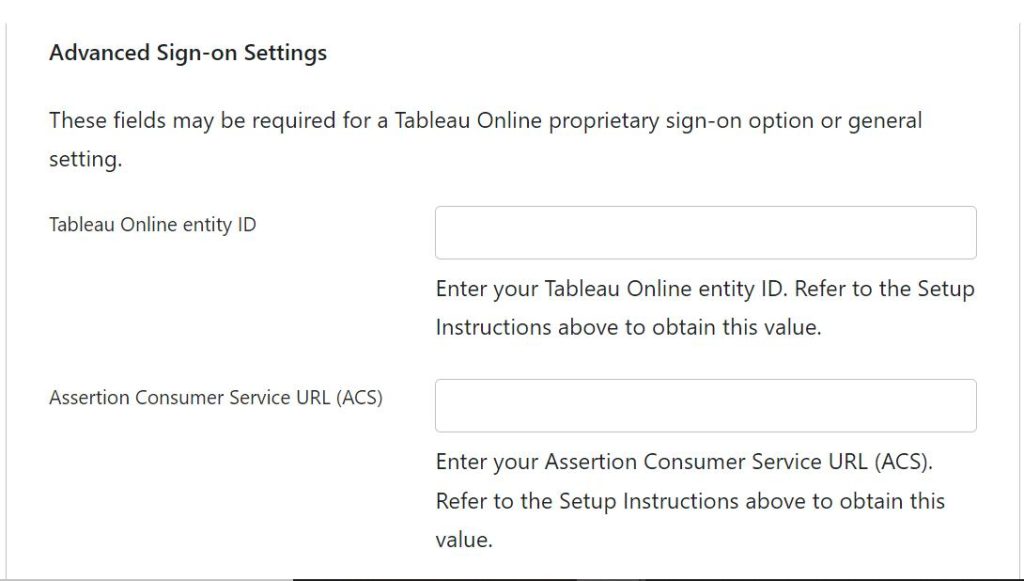
8. Return to the Okta administrator console general settings and paste the URL into the corresponding fields and click Save.
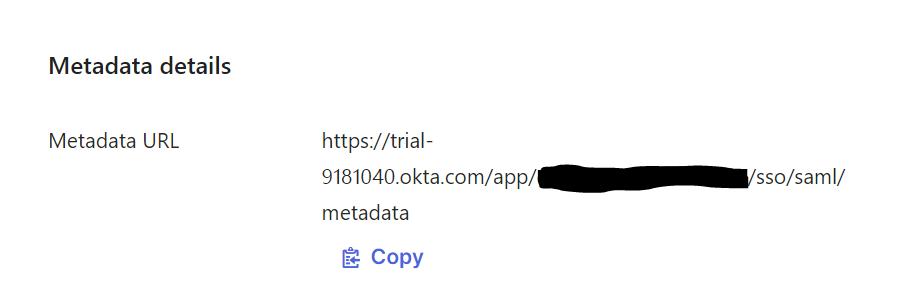
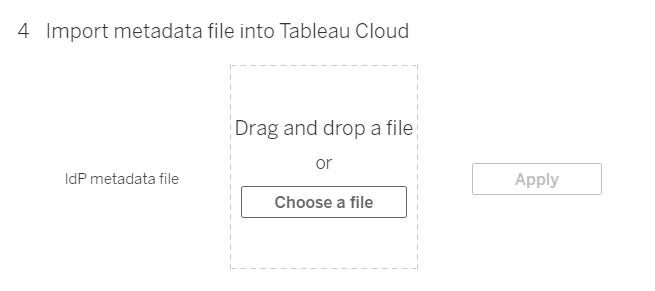
9. Copy the metadata URL and open new tab and save it as an XML file.
10. Switch to Tableau Cloud tab and import the same metadata file into Tableau Cloud and Click Apply.
Setting Up SCIM for User Management
Okta can be used for user management, provision groups, and assigning Tableau Cloud site roles.
1. After adding Tableau Cloud to the OKTA application, remain signed into both the Okta console and Tableau Cloud, by following the below steps:
- In Tableau Cloud, the Settings > Authentication page.
- In the Okta Developer Console, Applications > Tableau Cloud > Provisioning.
2. On the Authentication page in Tableau Cloud, under Automatic Provisioning and Group Synchronization (SCIM), select the Enable SCIM check box and Generate New Secret.
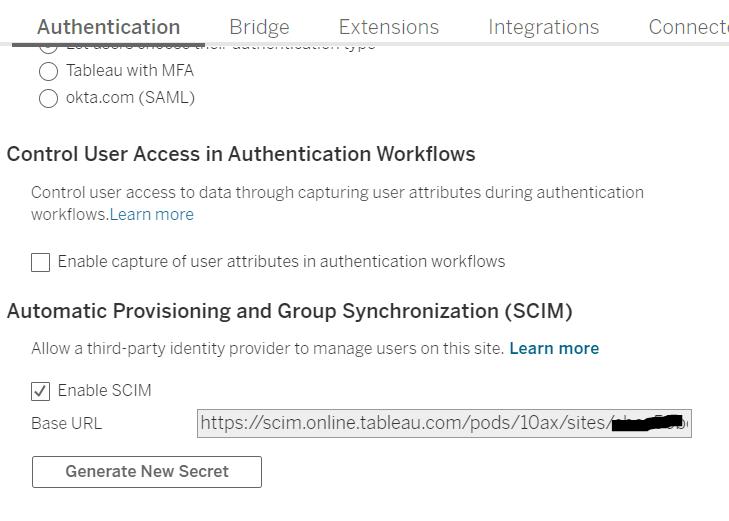
3. Copy the secret token value, and then on the Provisioning page in your Okta administrator console, select API Integration in the Settings column.
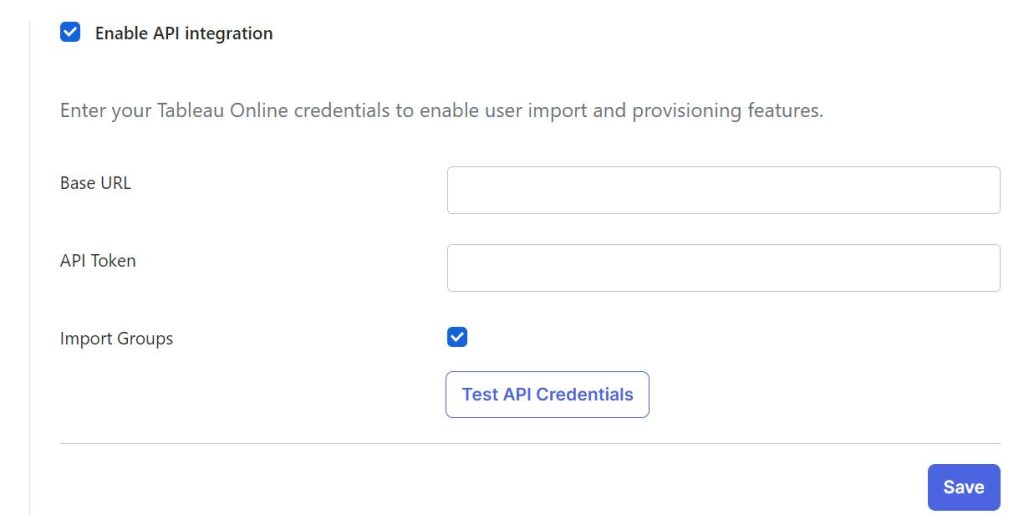
4. Select Edit, and then do the following:
- Select the Enable API integration check box.
- For API Token, paste the Tableau Cloud SCIM secret token you copied in the previous step.
- For Base URL, copy and paste the Base URL shown in the Tableau Cloud SCIM settings.
5. Select To App from the left pane setting option and click Edit, after that select Create Users, Update User Attributes and Deactivate Users check box.
User provisioning and Group synchronization
Simplifying User Management with Okta and Tableau
User provisioning from Okta to Tableau involves setting up a connection between your Okta identity management system and Tableau for seamless user management and access control. This integration streamlines the process of creating, updating, and deactivating user accounts in Tableau based on changes made in Okta. Here’s how you can achieve this:
1. Create one Active Directory (AD) group for each site role (e.g. Creator, Explorer, Viewer, Unlicensed etc.).
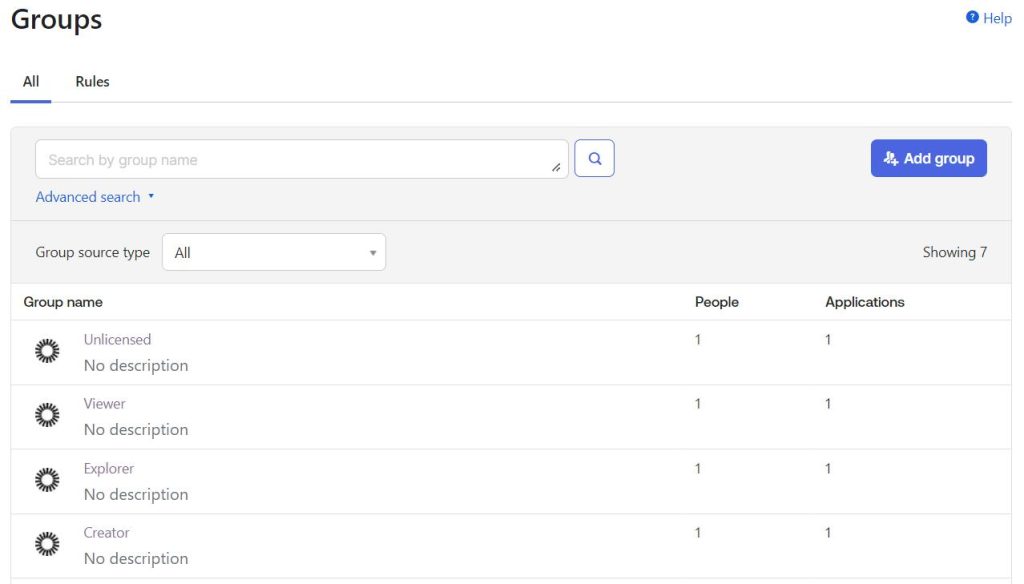
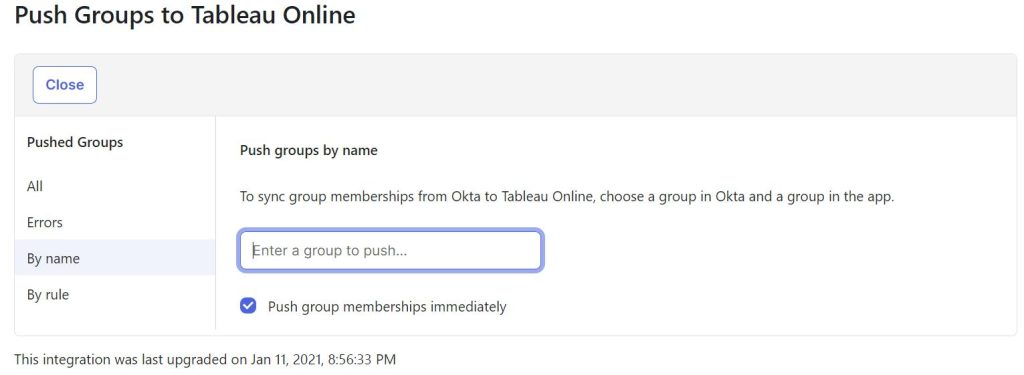
2. Sync these Okta groups with Tableau for automatic user flow. (note: make sure that the push group memberships immediately option is selected.)
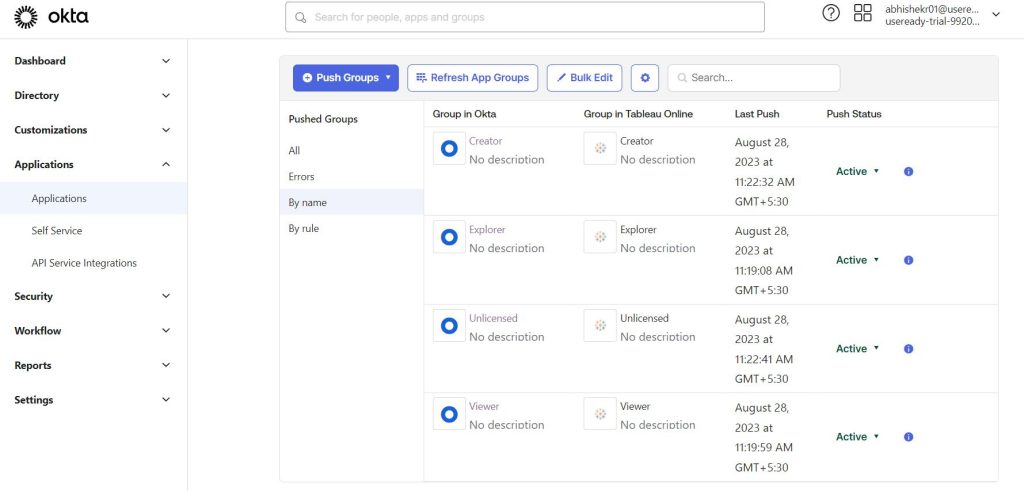
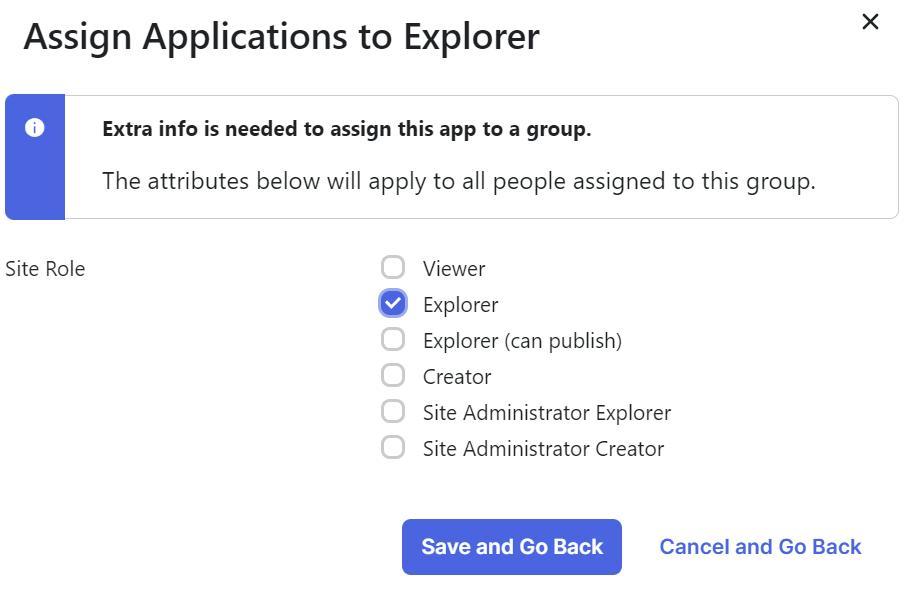
3. After this assign each site-based AD group to the Tableau cloud with corresponding site role.
4. As per requirement, new users will be added to the site-based AD groups.
5. Now to change the site role of a particular user we can move that user (remove from the existing group and add it into the requested site-based group) from one group to another and the corresponding site role will reflect in Tableau cloud.
6. If a user is part of two or more AD groups, the most permissive site roles will be reflected in Tableau. That said, it is not advisable to keep any user in more than one role-based AD group.
Adding the custom attribute “Unlicensed” site role
By default, Okta does not provide an Unlicensed site role and therefore we have to add it as a custom attribute.
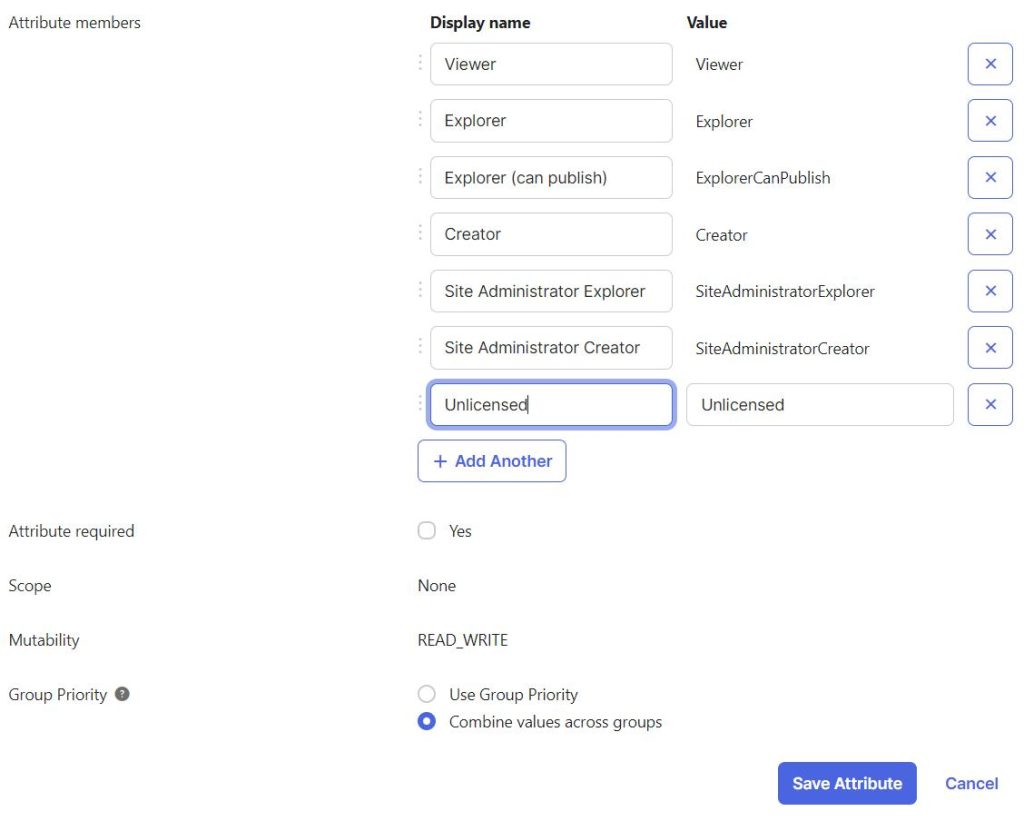
If the User is pushed with an unlicensed site role, then to change their site role, then remove the user from the Unlicensed Group, remove the same user from the Tableau cloud, and then add it to the requested site-based group.
As the user will be deactivated from the OKTA then automatically site role will be changed to “Unlicensed” and once that user is reactivated the previous site role will get reinstated.
Advantages of Integrating Okta with Tableau
Integrating Okta with Tableau is a smart move that offers a number of advantages including:
- Multi-factor authentication with secure data transmission
- Seamless user provisioning and de-provisioning
- Implementing role-based access control (RBAC) in Tableau
- Monitoring user activities in Tableau
- Auditing and compliance with Okta’s reporting capabilities
- Efficient handling of increased user loads
- Potential enhancements such as automated user onboarding
Conclusion: A Secure and Streamlined User Experience
Elevate Your Security with Okta Tableau Integration
By leveraging Okta’s powerful IAM capabilities, organizations can ensure that Tableau users have the timely and right access to the data they need. By integrating Okta, security admins can say goodbye to password headaches and in its place have a more secure and efficient mechanism for managing user access to Tableau.









 Media Coverage
Media Coverage Press Release
Press Release